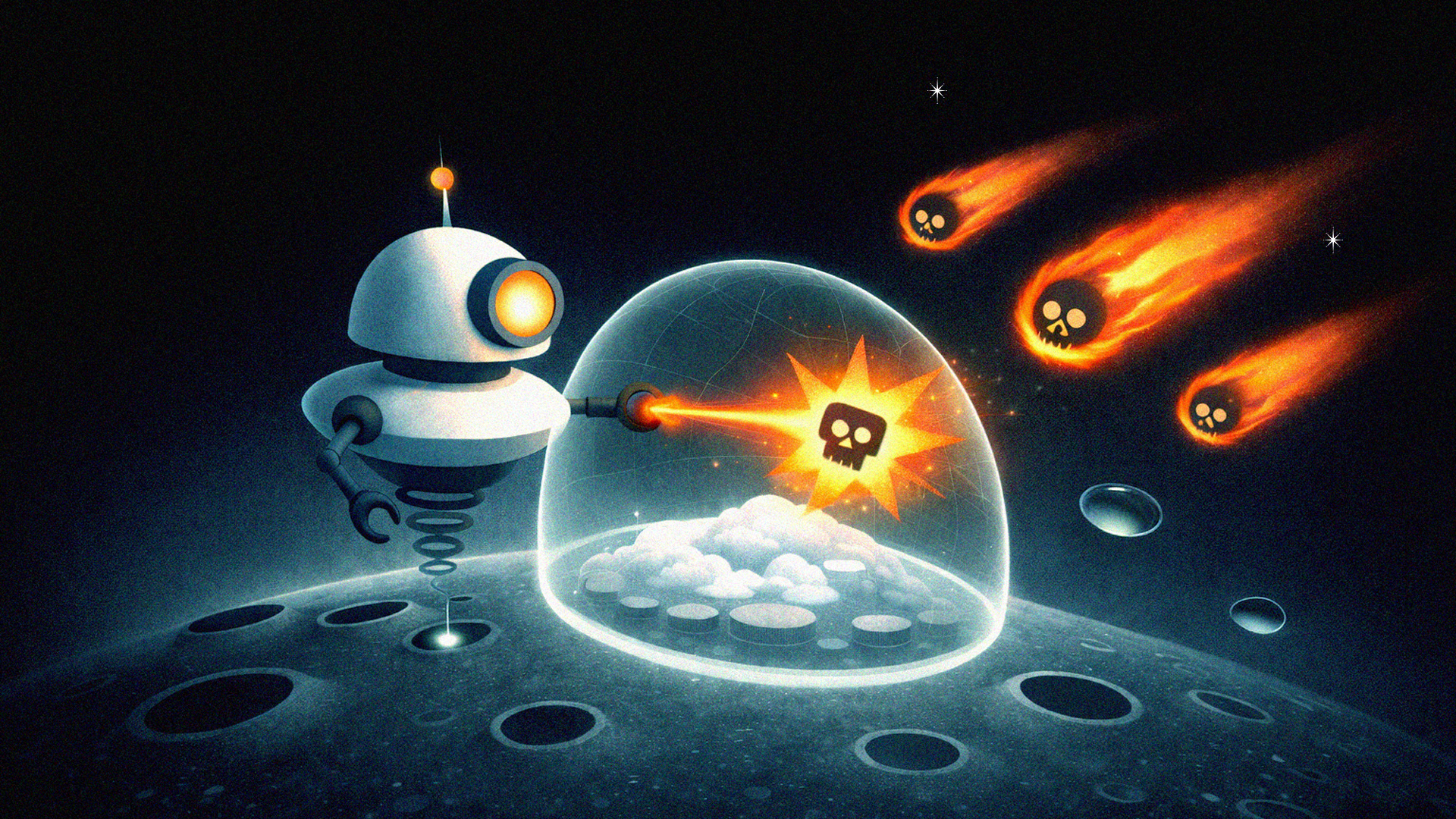
Last year, we introduced Eon’s ransomware protection package, the first end-to-end solution designed for the cloud. Today, we’re building on that foundation by extending ransomware detection to databases, expanding protection beyond VMs and object storage.
Eon is the first backup platform to analyze the logical contents of database backups, enabling automatic detection of ransomware, corruption, and anomalous behavior to help maintain backup integrity across the entire backup and recovery lifecycle.
Backup Infrastructure Has Become a Primary Target
Ransomware attacks are projected to cost businesses $265 billion annually by 2031, and attackers increasingly target backup infrastructure to eliminate recovery options.
Instead of focusing only on production systems, attackers now attempt to compromise the recovery layer itself by:
- Deleting recovery points
- Encrypting backup data
- Corrupting database records
- Embedding ransomware notes inside stored datasets
Traditional detection approaches struggle in modern cloud-native environments. Most rely on scanning files or disk volumes using entropy analysis or signature matching, techniques designed for workloads running inside virtual machines.
However, modern database services do not expose filesystem-level backup files. This creates a growing visibility gap, making it difficult to proactively detect malicious activity within databases before recovery.
How Eon Detects Ransomware Inside Databases
Eon closes this visibility gap by analyzing the logical contents of database backups. Instead of scanning storage files, the platform evaluates structured data elements such as tables, rows, schema definitions, and value distributions to identify indicators of ransomware activity or corruption.
Signals analyzed include:
- Sudden drops in row or table counts
- Unexpected schema changes
- Cardinality shifts caused by encrypted values
- Data corruption patterns
- Ransomware notes embedded within stored datasets
Each signal contributes to a weighted confidence score, allowing Eon to correlate multiple indicators before flagging a backup as potentially compromised. This multi-signal detection model reduces false positives while improving detection accuracy.
When anomalies are detected, detailed explanations are surfaced directly in the Eon console so operators can quickly understand what changed between backup versions and determine whether a recovery point is reliable.

Key benefits of Eon's Ransomware Detection for Databases
This approach provides several advantages for organizations with cloud-native workloads:
Cloud-Native Architecture
Eon’s ransomware detection package is built for cloud infrastructure. Unlike legacy backup systems that rely on agents and appliances, Eon uses a cloud-native architecture that integrates directly with cloud provider APIs, reducing the additional attack surface created by agent-based systems.
Immutable, Logically Air-Gapped Protection
Backups are stored in immutable, logically air-gapped vaults that prevent attackers from modifying or deleting recovery data, even if production systems are compromised. Eon’s approach aligns with all five functions of the NIST Cybersecurity Framework (NCF), rather than focusing only on protection and recovery.
Fast, Granular Recovery
Eon enables granular exploration and recovery of backup data, allowing teams to isolate clean recovery points and restore only the specific data required (e.g. individual tables or objects) rather than performing full environment restores. This precision recovery model helps organizations minimize downtime and restore services faster after an incident.
End-to-End Detection Across Workloads
With this release, Eon’s ransomware protection package now provides detection coverage across the full backup surface:
- VMs: Detection includes file entropy analysis, ransomware extensions, filesystem behavior patterns, malware signatures, and embedded ransomware notes.
- Object Storage: Eon detects mass deletion events, abnormal access patterns, and object integrity anomalies.
- Databases: Detection focuses on structured data signals including row and table count deviations, schema changes, cardinality shifts, and corruption indicators for databases including Postgres, MSSQL, MySQL, RDS.
Learn more
Ransomware detection for databases is currently in early access, while existing support for VMs and object storage resources remains generally available. Schedule a demo to learn more and see how Eon delivers secure, cloud-native backup and ransomware protection across your cloud infrastructure.
Frequently Asked Questions
What databases does Eon support for ransomware detection?
Eon analyzes backups from both managed and self-hosted databases, including PostgreSQL, MySQL, Microsoft SQL Server, RDS, DynamoDB, and others.
How does Eon detect ransomware inside database backups?
Eon analyzes the logical contents of database backups rather than scanning files or disks. The platform evaluates tables, rows, schema definitions, and value distributions to identify anomalies that may indicate ransomware activity or corruption.
Examples include:
- Sudden drops in row or table counts
- Unexpected schema modifications
- Cardinality shifts caused by encrypted values
- Data corruption patterns
- Ransomware notes embedded within datasets
Multiple signals are correlated to produce a confidence score, improving detection accuracy and reducing false positives.
Why can’t traditional ransomware detection tools analyze database backups?
Most ransomware detection tools operate at the filesystem or disk level, scanning files for entropy changes or malware signatures. Managed database services do not expose backup files in this way, which creates a visibility gap. Eon addresses this by analyzing the structured data inside database backups, enabling detection that traditional approaches cannot provide.
Does this require agents or changes to database infrastructure?
No. Eon’s detection capabilities operate through its cloud-native backup architecture and integrate directly with cloud provider APIs. No agents, appliances, or infrastructure changes are required.








.png)
.png)