Why ransomware goes after cloud backups first
Ransomware crews don’t stop at production data anymore. They go after backups early because backups decide whether you recover fast or pay. I see the same pattern behind a lot of cloud incidents. Once attackers gain access, they not only encrypt data but also target the recovery path.
Attackers usually get in through stolen credentials, weak IAM controls, or backup systems that sit too close to production.
From there, they:
- Shorten retention
- Queue deletions
- Change lifecycle rules
- Wipe backup copies across accounts and regions
Some groups also hit network-accessible backup volumes through the same control plane as production. By the time your staff starts a restore, the clean copy is already gone.
Cloud backups stay exposed when a single admin account can access production and backup data, when access is too broad, or when immutability and separation don’t hold. Backup security can’t stop at storage durability.
Eon treats backup protection as part of ransomware defense because recovery only works when attackers can’t alter, delete, or quietly age out the data you need most.
Why your backups fail during ransomware attacks
Backups usually fail before anyone starts a restore. Ransomware crews know that recovery is the real threat to their payout, so they target backup access, backup policy, and backup copies early. I see the same weak points come up again and again.
Backup access sits too close to production
Many teams keep backups in the same account, the same network path, or the same control plane as production. One stolen credential can open both sides at once.
Recovery falls apart when the backup path shares the same blast radius as the live environment.
Delete and retention controls are too weak
A backup isn’t safe just because it exists. Attackers look for ways to shorten retention, queue deletions, or change lifecycle rules before anyone notices. Immutability and tight delete controls matter because they decide whether backup data survives the attack.
Coverage drifts as the cloud changes
Cloud environments don’t stand still. New accounts, regions, and services show up fast, while old scripts and tag rules fall behind. Gaps stay hidden until a team tries to recover a workload that never had the right protection in the first place.
Restore testing doesn’t match real incidents
A yearly restore drill won’t tell you much during a live attack. Small incidents need precise recovery, clean data, and known recovery times. Downtime grows fast when teams haven’t tested real restore paths under normal conditions.
No one can identify a clean recovery point fast
Recovery gets harder when teams can’t tell which backup copy is safe to use. Ransomware often corrupts data before encryption starts, so the latest copy may not be the right one. Pressure rises fast when staff have to guess instead of restoring with confidence.
Good backup protection should prove 5 things:
- Attackers can’t reach backup copies through the same path as production.
- Standard admin access can’t alter or erase protected backups.
- New workloads get covered as the environment changes.
- Restore tests happen often enough to trust the process.
- Recovery staff can find a clean restore point without guesswork.
Backups fail during ransomware attacks when isolation, policy, and recovery readiness break down simultaneously. Strong backup strategy closes those gaps before an attacker gets the chance.
6 best practices for cloud ransomware protection
Cloud ransomware protection starts before encryption. Recovery only works when attackers can’t reach or destroy the data you need most.
1. Isolate backup data from production access
Backup data shouldn’t sit behind the same access path as production. Separate accounts, tighter IAM controls, and narrower admin boundaries reduce the likelihood that a single compromised credential can access everything.
2. Enforce immutability and strict delete controls
Backups need protection from change and deletion, as well as storage durability. Immutability, retention locks, and limited delete rights help backups survive ransomware, insider errors, and misconfiguration changes.
3. Test recovery on a regular schedule
A backup isn’t useful until you prove you can restore from it. Teams should test granular recovery often enough to trust the process and measure real recovery speed against business needs.
4. Keep coverage aligned as the cloud changes
Cloud environments change fast. New accounts, regions, and services should fall under the backup policy as soon as they appear, or gaps will grow faster than most teams notice.
5. Protect copies across accounts and regions
Extra copies only help when attackers can’t reach all of them through the same path. Cross-account and cross-region separation make recovery more resilient when one environment gets compromised.
6. Keep evidence ready before an audit or incident
Security and compliance staff should be able to show backup coverage, retention, immutability, and restore testing without a manual scramble. Clear records make audits easier and make recovery claims more credible.
Ransomware defense isn't a single control; it spans detection, protection, and recovery working together. The NIST Cybersecurity Framework breaks this down into five functions.
Eon addresses all five:
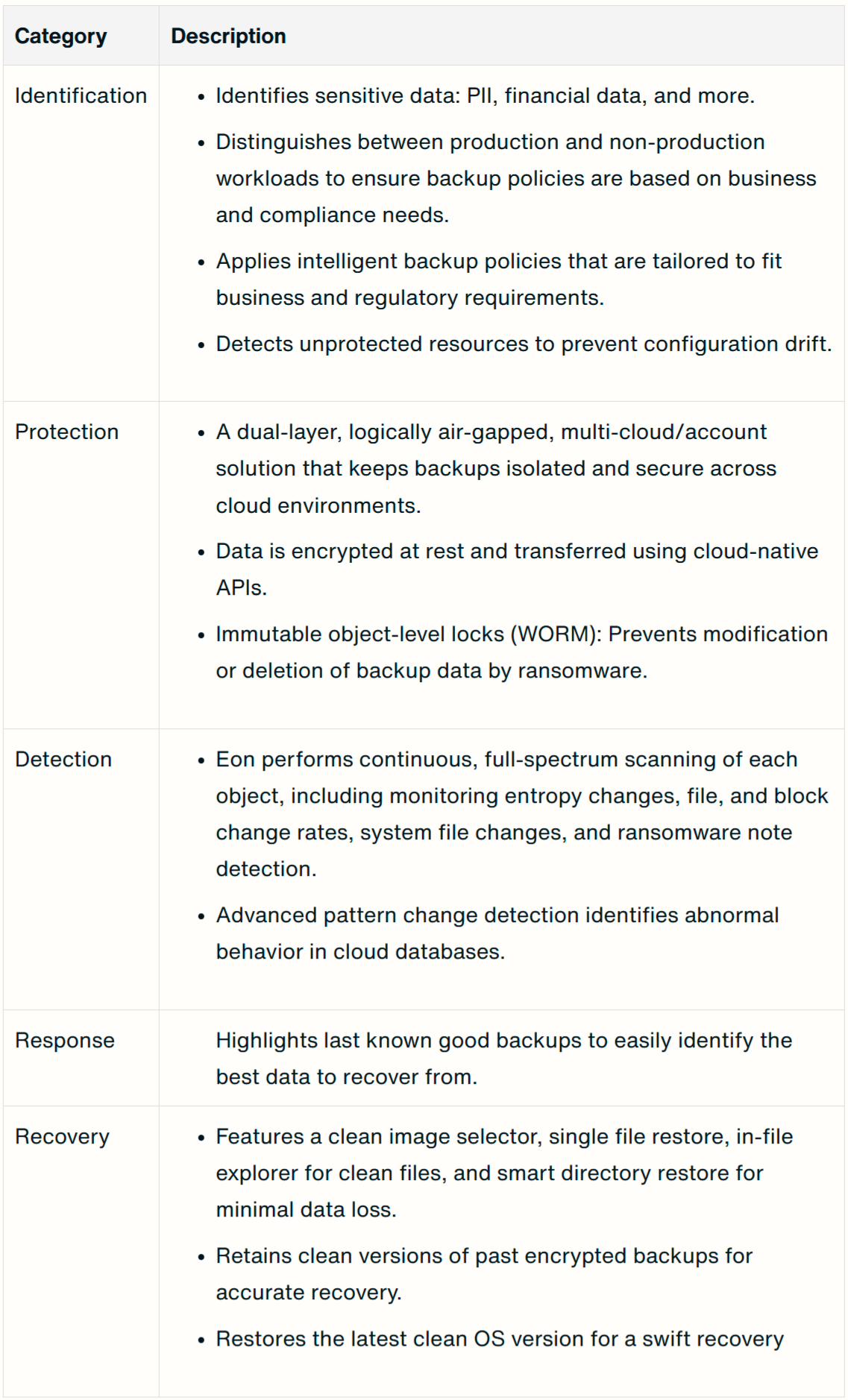
Together, these capabilities give teams a defensible, auditable ransomware posture, not just storage.
How to test your cloud backup recovery readiness
Having cloud backups doesn’t mean recovery will work. Most teams learn that too late, after ransomware hits and the restore path breaks.
I’d do these six things first:
- Verify immutability. Attempt to delete or modify a backup object using standard admin credentials. If you can do it, an attacker can too.
- Test cross-account and cross-region access. Confirm that your production account cannot reach your backup storage directly. Any shared access path gives attackers a way in.
- Run a granular restore. Pick a single file, database, or VM and restore it from backup. Measure how long it takes and whether the data is clean and complete.
- Check retention integrity. Review your retention policies across all accounts and regions. Look for unexpected changes to window lengths or scheduled deletions.
- Simulate a clean image restore. Use your clean image selector or an equivalent tool to confirm that you can quickly identify a ransomware-free restore point.
- Measure your actual RTO and RPO. Compare them against your targets. If there is a gap, that gap is your risk exposure.
Teams that test once a year leave too much to chance. Recovery readiness gets stronger when these checks become routine, not when they wait for an audit or an incident.
Does your cloud need ransomware protection?
Your cloud needs ransomware protection because attackers now target cloud data and backups directly. Your estate is large, fast-changing, and expensive to back up. Legacy backup tools drive up costs while recovery remains slow and risky.
Ransomware remains one of the most damaging threats to cloud workloads. Analysts estimate global ransomware damage will exceed USD 275 billion per year by 2031.
Cybersecurity agencies, including CISA and the UK's NCSC, have consistently flagged backup destruction as a core ransomware tactic and recommend immutable, isolated copies as a baseline defense.
Research reveals a second problem. Many organizations never fully recover after an attack. Victims fail to recover about 43% of data affected by ransomware, even when they pay and attempt restores.
Most on-premise and appliance-based solutions can't handle elastic cloud environments.
They struggle with:
- Rapidly changing cloud resource configurations
- Massive object stores in S3, GCS, and Azure Blob
- High-frequency, transactional data with strict RPO and RTO targets
Eon's cloud backup ransomware protection capabilities close this gap. We combine ransomware-resistant cloud backups with detection and targeted recovery, cutting both risk and recovery cost.
How does Eon protect cloud backups from ransomware?
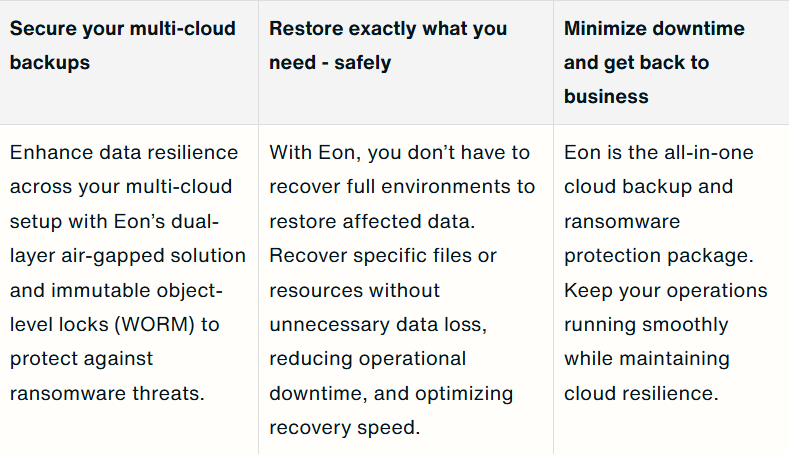
Eon protects cloud backups from ransomware at the backup layer itself. We treat backups as a high-value target, so protection has to cover storage, detection, and recovery.
Immutable, air-gapped backup storage
Eon protects backup data with immutable, logically air-gapped copies, tight access controls, and cross-account and cross-region isolation. One weak path shouldn’t give an attacker access to both production data and the backups you’d need to recover.
Threat detection tied to clean recovery points
Threat detection matters during a ransomware event because recovery depends on finding a clean backup fast. Traditional backup tools scan files, which leaves managed services like RDS, Aurora, and S3 largely invisible during an attack.
Eon analyzes the logical content of backup data to detect ransomware across managed databases, object storage, and VMs. Instead of relying on file-level signals, we analyze data at the logical layer across databases, objects, and workloads, giving full visibility into managed services.
We scan protected backups for ransomware signals, including:
- Entropy spikes
- Unusual change in data volume
- Ransom notes
- Abnormal file behavior
Monitoring runs against protected backup copies, so attackers can’t easily tamper with the data or shut off visibility. Detection findings link directly to clean recovery points, which helps your staff move from alert to restore much faster.
Granular recovery that cuts downtime and cost
Granular recovery matters during a ransomware event. Eon lets teams restore only the data the attack touched.
- Cuts downtime
- Lowers compute and egress costs
- Reduces the chance of putting encrypted data back into production
Real recovery depends on isolation, policy, and readiness holding up at the same time.
Together, these capabilities map directly to modern security standards.
Secure your cloud backups from ransomware with Eon
Attackers now go after your cloud backups before they touch production. They steal credentials, wipe snapshots, and change retention settings to destroy your recovery options before you even know an attack started.
Legacy backup tools can't handle this. They struggle with large, fast-changing cloud environments. And when something goes wrong, they force you to restore entire environments when you only need to recover a single file or database record.
Eon keeps your cloud backups air-gapped and immutable, which helps prevent attackers from altering or deleting protected recovery data.
Traditional vendors scan backup files, which leaves managed databases exposed. Eon analyzes the logical content of database backups to identify clean recovery points. We scan backup data around the clock for ransomware signals so you catch threats early.
When you need to recover, Eon restores only what ransomware hit (at the file, record, or table level) and nothing more.
Less downtime, lower recovery costs, and no risk of putting corrupted data back into production. Request a demo today and see how Eon protects your cloud backups from ransomware.
Frequently asked questions
What is cloud backup ransomware?
Cloud backup ransomware is malware that targets cloud backups instead of only production systems. It attacks, deletes, encrypts, or corrupts backup copies so your team cannot restore clean data.
How does cloud backup ransomware work?
Cloud backup ransomware works by abusing cloud credentials and APIs. It attacks change retention, deletes snapshots, or encrypts backup volumes before they encrypt production workloads.
Why do attackers target cloud backups?
Attackers target cloud backups because backups hold complete copies of critical data; destroying them removes your recovery options and forces higher ransom payments. No clean backup means no way out without paying.
Do regular cloud backups stop ransomware?
No, regular cloud backups alone do not stop ransomware. Cloud backups only stop ransomware when teams combine them with immutability, logical air gaps, and strong access controls.
Why doesn’t file-based scanning work for RDS, Aurora, or Cloud SQL?
File-based scanning does not work well for RDS, Aurora, or Cloud SQL because backups are stored in managed database formats instead of standard files you can inspect directly. Traditional tools scan backup files, which leaves managed databases exposed. Eon analyzes database-level data to identify clean recovery points.
How does Eon protect cloud backups from ransomware?
Eon protects cloud backups from ransomware with immutable, logically air-gapped storage and workload-aware ransomware detection across self-hosted and managed databases, object storage, and VMs. When recovery is needed, Eon restores only affected files, records, or tables.
Can Eon help reduce recovery time after ransomware?
Yes, Eon helps reduce recovery time after ransomware by allowing granular restores. Eon lets teams recover only the files, databases, or systems that were hit by ransomware, instead of rebuilding entire environments.
Does Eon work across multiple clouds and accounts?
Yes, Eon works across multiple clouds and accounts. Eon protects cloud backups in multi-account, multi-region environments so teams apply consistent ransomware protection to all critical data.