A strong cloud ransomware backup solution should do more than keep copies around. It should help security and infrastructure teams protect recovery points, detect compromise across modern workloads, identify clean recovery points, and recover the right data with the recovery scope the situation requires. That is where Eon stands apart from legacy backup tools.
Many teams still assume their current backup stack is good enough to withstand ransomware. That assumption usually holds until they need to answer hard questions under pressure.
Which recovery point is clean? What changed? Can we restore just the affected data? Can we trust the backup, or did the attack reach that too?
That is where older backup products start to show their age. Many were built to store copies and manage retention. They were not built for cloud workloads, cloud-scale change, or the recovery decisions teams need to make during a ransomware event.
Recent attacks made that gap harder to ignore. Codefinger and Storm-0501 reinforced the same point: attackers do not stop at production systems. They also target cloud data, storage, and backup paths. Those attacks expose the same kinds of backup gaps that ransomware exploits. When that happens, “we have snapshots” is not much of an answer.
Eon was built for that reality. It is a cloud-native platform for AWS, Azure, and Google Cloud that combines logical air gaps, immutable backups, Cloud Backup Posture Management (CBPM), ransomware protection, and granular recovery in a single platform.
What is a cloud ransomware backup solution?
A cloud ransomware backup solution helps teams protect backup data from tampering, detect signs of compromise, identify clean recovery points, and restore affected data after an attack.
That matters because having a backup is only the starting point. Teams also need to know whether the backup still looks trustworthy and whether they can recover exactly what the incident affected.
Why are legacy backups weak against ransomware?
Legacy backups are weak against ransomware because they treat backups as passive storage. They keep copies, but they do not do enough to help teams validate backup integrity, detect suspicious changes across cloud workloads, or recover with precision.
Four gaps come up again and again:
1. Backup copies may still sit too close to the attack path
A vault or snapshot can be durable and still be too exposed through shared credentials, APIs, or operational paths. That matters because attackers are not only targeting production systems. They are also targeting the backups you need to recover from.
2. Detection often stops at files and disks
That leaves big gaps in cloud environments, where critical data also lives in object storage and managed databases.
3. Teams still have to guess what is clean
During an incident, the job is restoring the right thing from a clean point in time. Many legacy tools leave too much of that work to manual investigation.
4. Recovery is often too broad
Rolling back a full system to recover a single file, object, or table creates additional downtime and operational pain.
How does Eon protect backups from ransomware?
Eon protects backups from ransomware by combining architecture, posture management, and detection.
At the architecture layer, Eon uses logically air-gapped, immutable backups. At the control layer, Eon uses CBPM to continuously discover resources, classify data, and enforce policy coverage without relying on manual tagging. At the detection layer, Eon surfaces signs of compromise across the workloads teams actually run.
That matters because ransomware protection is not only about locking down storage. It is also about finding gaps before an attacker does.
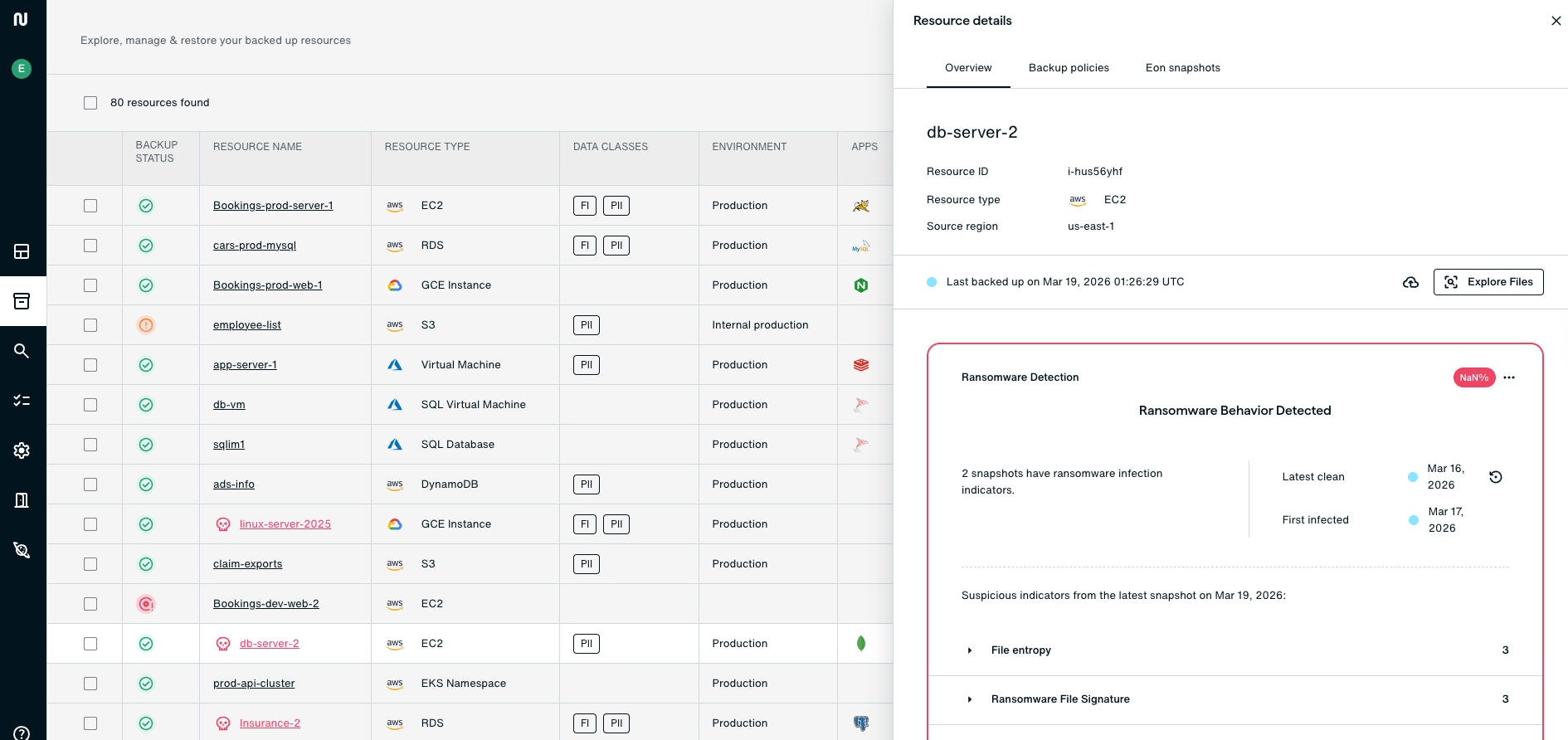
How does Eon detect ransomware across VMs, object storage, and databases?
Eon uses a multi-signal approach to detect ransomware, corruption, and anomalous change across backup data.
For virtual machines, Eon uses signals such as entropy analysis, known extensions, behavioral signals, ClamAV malware scanning, and ransom note detection. For object storage, it looks for mass deletions, anomalous access patterns, and object-level integrity issues. For databases, it analyzes database content to detect row-count anomalies, cardinality shifts, table deletions, and schema changes across managed and self-hosted databases.
That broader workload coverage matters because cloud environments are not just VMs anymore. If a ransomware backup platform cannot inspect object storage and databases in a meaningful way, it is missing a large part of the real attack surface.

Why is database ransomware detection different?
Managed databases do not expose backup data as normal files. That means file-based methods cannot properly inspect what changed inside the data.
Eon addresses this by analyzing database content to detect row-count anomalies, cardinality shifts, table deletions, and schema changes across managed and self-hosted databases, which is central to Eon’s ransomware detection for databases.
This is one of Eon’s strongest points of differentiation against legacy backup tools. Many of them can scan files. That does not help much when the workload you are trying to protect is a managed database.
How does Eon help teams recover from ransomware with more confidence?
Eon helps teams recover with more confidence by making it easier to identify clean recovery points and choose the right recovery scope for the incident.
In some cases, teams may choose a broader restore from a known-clean point. In others, a scoped recovery may be the better operational choice once the clean point is understood.
What smarter ransomware recovery looks like
- Detect suspicious changes in backup data.
- Review recovery points and identify a clean version.
- Choose the recovery scope that fits the incident, whether that means restoring from a broader clean point or performing a scoped restore where appropriate.
- Restore what is needed and validate the result.
That approach reduces downtime and keeps the recovery process from becoming its own incident.
How does Eon reduce compliance and cyber resilience risk?
Eon reduces compliance and cyber resilience risk by helping teams keep coverage consistent, retention controlled, and recovery evidence easier to trust.
CBPM plays a big role here. It helps teams continuously discover resources, classify data, and apply backup policies across the environment. That reduces the odds of finding uncovered data, weak retention settings, or policy drift during a real incident.
Eon also aligns its ransomware protection story to the five functions of NIST CSF 2.0: Identify, Protect, Detect, Respond, and Recover.
How does Eon compare with legacy competitors and native tools?
The biggest difference is that Eon was built for cloud workloads and recovery workflows, whereas many legacy products were later adapted to them.
Buyers comparing Eon against older backup vendors are usually not asking whether those tools can store backups. They are asking whether those tools can support cleaner, faster, more trustworthy ransomware recovery in the cloud. For a broader side-by-side view, see cloud backup alternatives.
Backups are no longer the fallback plan
Recent cloud ransomware activity made one thing clear: backups are no longer just the fallback plan. They are part of the attack path.
So if you are comparing Eon with legacy ransomware backup products, the real decision is not about who can keep a copy around. It is about who can help your team trust that copy, spot trouble sooner, and recover the right clean data with less guesswork.
That is where Eon is stronger.
Book a demo to see how Eon helps security and infrastructure teams improve ransomware readiness and recover clean data faster, or see how SoFi improved resilience with Eon.
FAQ
Do I really need more than immutable backups?
Yes. Immutability matters, but teams still need to know whether recovery points look clean and whether they can restore the right data fast. Eon adds logical air gaps, detection, posture management, and granular recovery on top of immutable storage.
What is a logical air gap?
A logical air gap is a cybersecurity strategy that separates critical data or backups from the main network through software, network segmentation, and security policies, rather than through physical disconnection. It is designed to reduce the chance that attackers or compromised credentials can tamper with backups.
Can backup software detect ransomware in managed databases?
It can if the platform can inspect the logical content of database backups. Eon does that, which helps it catch compromise and corruption that file-based methods miss.
What kinds of database issues can Eon detect?
Eon detects row-count anomalies, cardinality shifts, table deletions, and schema changes across managed and self-hosted databases.
Does Eon protect object storage too?
Yes. Eon’s ransomware protection also covers object storage, where it can surface signals such as mass deletions, anomalous access patterns, and object-level integrity issues.
How does granular recovery help during a ransomware incident?
Granular recovery can help when teams have already identified a clean recovery point and want to restore a specific file, object, or table without restoring more than necessary. In higher-risk scenarios, teams may still choose a broader recovery from a known-clean point.
How does Eon help with compliance and cyber resilience?
Eon helps teams keep backup policies consistent, maintain retention and immutability controls, and improve auditability across the cloud estate. CBPM is a key part of that story.
How is Eon different from native cloud snapshots?
Native snapshots can store recovery points, but they do not automatically give teams the same posture management, database-aware anomaly detection, or granular recovery workflow described here.
Is this useful if we already have a legacy backup product?
Yes, if that product leaves gaps in cloud workload coverage, backup integrity validation, or scoped recovery. That is often where cloud teams start to feel the limits of older backup designs.
What should I validate before a ransomware event happens?
Validate that backups are immutable, logically separated, that policy coverage is complete, that recovery points can be trusted, and that scoped recovery is possible for critical workloads.

.jpg)





.png)
.png)